In the open space production room, large windows projected beams of green-blue light onto the white desks arranged in an orderly checkerboard pattern, protected by transparent plexiglass panels, now empty for the lunch break.
Mostly programmers and analysts worked in that place, while the office just above, delimited by glass walls, was reserved for the chief engineer. Mark worked in the server room in the basement, an inaccessible place protected by security systems, constantly illuminated by neon lights.
He shared his cramped office with two other system administrators and the IT systems manager:they monitored the technological heart of the company, where infinite LED lights pulsation merged with the perennial artificial light reflected on the cold metal cabinets, immense bastions full of electronic devices, servers, switches, and other demons powered by the constant breathing of thousands of fans, modern infernal forges where the knowledge of the new millennium was produced, transformed, and transmitted.
The sky was constantly hidden from view, as were the temperature, humidity, and airborne dust, all perfectly controlled, so nature and seasons had no meaning there, dispersed in an electronic dream without time or destiny.

Just a year earlier, working in that place would have been a dream come true for Mark, a dream that had turned into a sad prison without bars.
Controlling the systems was his job, but perhaps it was the system that controlled his life, which he realized in the first year of work, after the bad adventure that had seen him guilty of poor security management in the company.
He wasn’t fired, but he certainly didn’t look good.
He often thought of Michelle… strange girl.
He felt guilty for the rebuke, for having reported her to the police. After all, if he had stopped that hacker attack before it happened, it wouldn’t have been so traumatic.
Instead, he wanted to play, set a trap, and catch the hackers in the act after tracing them: what a satisfaction that would have been!
But he had not taken into account that Michelle was the enemy.
When Mark received her phone call, he knew the game was up, and with a heavy heart, he reported her. Nothing would ever be the same again: now Mark secretly hoped to meet Michelle again somehow, not just to talk about Stallman or the Open Source software philosophy.
That desk in the back left near the windows in the development room, was the workstation where Michelle had worked.
With the excuse of checking a PC in the production room during lunch break, Mark had gained access to the room at a time when it should have been almost empty to act undisturbed. The desk had not been used anymore, everything had been removed, and the same PC had been unused for at least two months. Sitting at the workstation, Mark turned it on, waited for the boot process to complete, and there was the request for the password. The system suggested access to Michelle, whose password was no longer valid since her account had been removed from the server, which indirectly confirmed that the PC had not been used since Michelle left.
Change user, access as administrator… password entry… logged in.
Obviously, Mark followed the user accounting, so he had the administrator credentials.
“Can you explain to me what you are doing?”
It was the production manager, Engineer Fenninger, who had stayed for lunch in his office and Mark had not noticed him.
“I don’t remember requesting any system intervention.”
“We have detected an anomaly in the network logs and I asked my boss, Martin, to come and check.”
“No one has used that PC since Michelle left.”
Said Fenninger.
“I confirm, the account and all its data have been removed from the server, yet we have noticed the presence of this machine’s MAC address in the logs of these nights.”
“A turned-off PC…”
“Exactly, however, the system has reported strange activity. I just wanted to check the log of this PC and also verify the possible configuration of wake-on-LAN in the BIOS… Can I take it for maintenance?”
“Okay, go ahead. That machine is no longer needed. I’ll be waiting for a report and… reset the system from scratch with the new version.”
“Thank you, it will be done.”
Mark felt relieved. He had come up with a plausible excuse and the manager, perhaps due to carelessness and lack of expertise in systems, or perhaps because he had other things on his mind, had believed him.
Mark was looking for Michelle. Michelle was, in fact, the actual victim. The Moloch of Hi-Tech had deceived, disappointed, and devoured her. And Mark had been the executor of it all.
He had tried in vain to contact her by email, phone, social media, chat, and forums she frequented. She was probably convicted or maybe detained… he had not followed the judicial proceedings… but why? Michelle had caused no harm. The system had defended itself well, and all the data she had stolen was garbage. Was it attempted fraud or attempted hacking? The damage suffered by the company was negligible. In fact, they had boasted of thwarting a hacking attack with their cutting-edge systems.
So much falsehood, so much injustice, so much hypocrisy, and such a waste of human resources.
Mark missed Michelle. Michelle was in his thoughts, his memories, his dreams. “… If you change your mind, you know how to contact me …” Those were his last words. Then the void, the sadness, the grayness of everyday life.
“Where are you, silent soul, reveal to me the beauty of your solitude.
Lost in the void of existence, your memory shatters my certainties,
I breathe thinking of your world.
I stole your freedom,
I destroyed dreams that only now I realize
… I never understood. “
One by one, he opened the drawers of the desk, empty, they had been emptied thoroughly…
actually no: opening the last drawer he felt that something was left at the bottom.
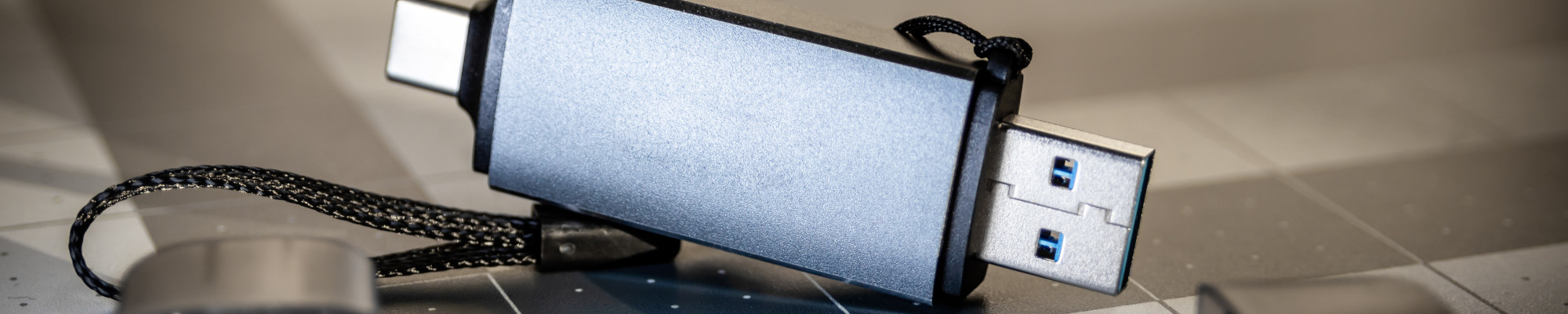
A small USB key, he recognized it immediately, it was the one Michelle used to carry around to use Linux anywhere, a practice that was obviously prohibited, at least in the company. He immediately hid it in his pocket, turned off the computer, disconnected it from the network, from the monitor, from all other devices, and took it to the laboratory for maintenance.
Mark was now happy. He felt silly, but that USB key could contain the clues he was looking for, that he hoped for…
(to be continued…)
PS: The story reveals a series of aspects related to computer security, we will talk about it soon. See the previous episode.
Greetings from the dark web
ANOM